CCNA 3 v7 Final Exam
1. Which design feature will limit the size of a failure domain in an enterprise network?
- the purchase of enterprise equipment that is designed for large traffic volume
- the installation of redundant power supplies
- the use of a collapsed core design
- the use of the building switch block approach
2. Which two things should a network administrator modify on a router to perform password recovery? (Choose two.)
- the system image file
- the NVRAM file system
- the configuration register value
- the startup configuration file
- system ROM
3. What type of network uses one common infrastructure to carry voice, data, and video signals?
- borderless
- converged
- managed
- switched
4. What are three advantages of using private IP addresses and NAT? (Choose three.)
- hides private LAN addressing from outside devices that are connected to the Internet
- permits LAN expansion without additional public IP addresses
- reduces CPU usage on customer routers
- creates multiple public IP addresses
- improves the performance of the router that is connected to the Internet
- conserves registered public IP addresses
5. Which two scenarios are examples of remote access VPNs? (Choose two.)
- All users at a large branch office can access company resources through a single VPN connection.
- A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ.
- A toy manufacturer has a permanent VPN connection to one of its parts suppliers.
- A mobile sales agent is connecting to the company network via the Internet connection at a hotel.
- An employee who is working from home uses VPN client software on a laptop in order to connect to the company network.
6. What are three benefits of cloud computing? (Choose three.)
- It utilizes end-user clients to do a substantial amount of data preprocessing and storage.
- It uses open-source software for distributed processing of large datasets.
- It streamlines the IT operations of an organization by subscribing only to needed services.
- It enables access to organizational data anywhere and at any time.
- It turns raw data into meaningful information by discovering patterns and relationships.
- It eliminates or reduces the need for onsite IT equipment, maintenance, and management.
7. What is a characteristic of a single-area OSPF network?
- All routers share a common forwarding database.
- All routers have the same neighbor table.
- All routers are in the backbone area.
- All routers have the same routing table.
8. What is a WAN?
- a network infrastructure that spans a limited physical area such as a city
- a network infrastructure that provides access to other networks over a large geographic area
- a network infrastructure that provides access in a small geographic area
- a network infrastructure designed to provide data storage, retrieval, and replication
9. A network administrator has been tasked with creating a disaster recovery plan. As part of this plan, the administrator is looking for a backup site for all of the data on the company servers. What service or technology would support this requirement?
- data center
- virtualization
- dedicated servers
- software defined networking
10. Which type of OSPF packet is used by a router to discover neighbor routers and establish neighbor adjacency?
- link-state update
- hello
- database description
- link-state request
11. Which two statements are characteristics of a virus? (Choose two.)
- A virus has an enabling vulnerability, a propagation mechanism, and a payload.
- A virus can be dormant and then activate at a specific time or date.
- A virus provides the attacker with sensitive data, such as passwords.
- A virus replicates itself by independently exploiting vulnerabilities in networks.
- A virus typically requires end-user activation.
Explanation: The type of end user interaction required to launch a virus is typically opening an application, opening a web page, or powering on the computer. Once activated, a virus may infect other files located on the computer or other computers on the same network.
12. Which public WAN access technology utilizes copper telephone lines to provide access to subscribers that are multiplexed into a single T3 link connection?
- ISDN
- DSL
- cable
- dialup
13. A customer needs a metropolitan area WAN connection that provides high-speed, dedicated bandwidth between two sites. Which type of WAN connection would best fulfill this need?
- packet-switched network
- Ethernet WAN
- circuit-switched network
- MPLS
14. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use debuggers?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
- to obtain specially designed operating systems preloaded with tools optimized for hacking
- to detect any evidence of a hack or malware in a computer or network
15. Consider the following output for an ACL that has been applied to a router via the access-class in command. What can a network administrator determine from the output that is shown?
R1# Standard IP access list 2 10 permit 192.168.10.0, wildcard bits 0.0.0.255 (2 matches) 20 deny any (1 match)
- Two devices connected to the router have IP addresses of 192.168.10. x .
- Two devices were able to use SSH or Telnet to gain access to the router.
- Traffic from one device was not allowed to come into one router port and be routed outbound a different router port.
- Traffic from two devices was allowed to enter one router port and be routed outbound to a different router port.
Explanation: The access-class command is used only on VTY ports. VTY ports support Telnet and/or SSH traffic. The match permit ACE is how many attempts were allowed using the VTY ports. The match deny ACE shows that a device from a network other than 192.168.10.0 was not allowed to access the router through the VTY ports.
16. What command would be used as part of configuring NAT or PAT to clear dynamic entries before the timeout has expired?
- clear ip dhcp
- clear ip nat translation
- clear access-list counters
- clear ip pat statistics
17. What are two characteristics of video traffic? (Choose two.)
- Video traffic consumes less network resources than voice traffic consumes.
- Video traffic latency should not exceed 400 ms.
- Video traffic is more resilient to loss than voice traffic is.
- Video traffic requires a minimum of 30 kbs of bandwidth.
- Video traffic is unpredictable and inconsistent.
18. Refer to the exhibit. A technician is configuring R2 for static NAT to allow the client to access the web server. What is a possible reason that the client PC cannot access the web server?
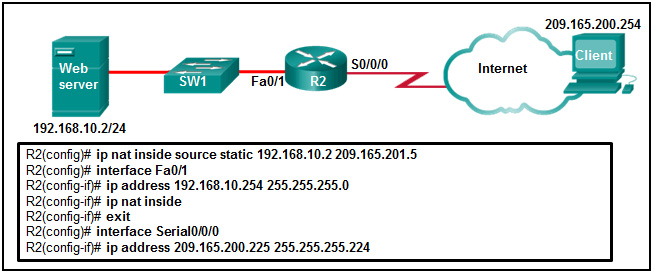
- The IP NAT statement is incorrect.
- Interface Fa0/1 should be identified as the outside NAT interface.
- Interface S0/0/0 should be identified as the outside NAT interface.
- The configuration is missing a valid access control list.
Explanation: Interface S0/0/0 should be identified as the outside NAT interface. The command to do this would be R2(config-if)# ip nat outside.
19. In setting up a small office network, the network administrator decides to assign private IP addresses dynamically to workstations and mobile devices. Which feature must be enabled on the company router in order for office devices to access the internet?
- UPnP
- MAC filtering
- NAT
- QoS
Explanation: Network Address Translation (NAT) is the process used to convert private addresses to internet-routable addresses that allow office devices to access the internet.
20. A data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?
- online collaboration
- BYOD
- virtualization
- maintaining communication integrity
21. Refer to the exhibit. Which address or addresses represent the inside global address?
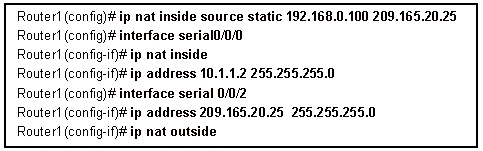
- 192.168.0.100
- 10.1.1.2
- any address in the 10.1.1.0 network
- 209.165.20.25
22. Which two IPsec protocols are used to provide data integrity?
- MD5
- DH
- AES
- SHA
- RSA
Explanation: The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm used for key exchange. RSA is an algorithm used for authentication.
23. If an outside host does not have the Cisco AnyConnect client preinstalled, how would the host gain access to the client image?
- The Cisco AnyConnect client is installed by default on most major operating systems.
- The host initiates a clientless VPN connection using a compliant web browser to download the client.
- The host initiates a clientless connection to a TFTP server to download the client.
- The host initiates a clientless connection to an FTP server to download the client.
Explanation: If an outside host does not have the Cisco AnyConnect client preinstalled, the remote user must initiate a clientless SSL VPN connection via a compliant web browser, and then download and install the AnyConnect client on the remote host.
24. A company is considering updating the campus WAN connection. Which two WAN options are examples of the private WAN architecture? (Choose two.)
- leased line
- cable
- digital subscriber line
- Ethernet WAN
- municipal Wi-Fi
25. Which type of QoS marking is applied to Ethernet frames?
- IP precedence
- DSCP
- ToS
- CoS
26. Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two.)
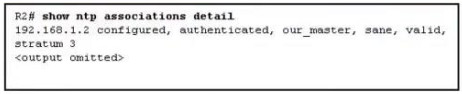
- Both routers are configured to use NTPv2.
- Router R1 is the master, and R2 is the client
- The IP address of R2 is 192 168.1.2.
- Router R2 is the master, and R1 is the client
- The IP address of R1 is 192.168.1.2
Explanation: With the show NTP associations command, the IP address of the NTP master is given.
27. Refer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server. Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)
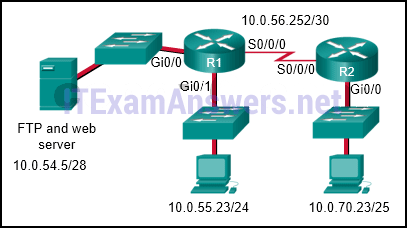
R1(config)# interface s0/0/0
R1(config-if)# ip access-group 105 out
R2(config)# interface gi0/0
R2(config-if)# ip access-group 105 in
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq www
access-list 105 deny ip any host 10.0.54.5
access-list 105 permit ip any any
access-list 105 permit ip host 10.0.70.23 host 10.0.54.5
access-list 105 permit tcp any host 10.0.54.5 eq www
access-list 105 permit ip any any
R1(config)# interface gi0/0
R1(config-if)# ip access-group 105 out
access-list 105 permit tcp host 10.0.54.5 any eq www
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
Explanation: The first two lines of the ACL allow host 10.0.70.23 FTP access to the server that has the IP address of 10.0.54.5. The next line of the ACL allows HTTP access to the server from any host that has an IP address that starts with the number 10. The fourth line of the ACL denies any other type of traffic to the server from any source IP address. The last line of the ACL permits anything else in case there are other servers or devices added to the 10.0.54.0/28 network. Because traffic is being filtered from all other locations and for the 10.0.70.23 host device, the best place to put this ACL is closest to the server.
28. Refer to the exhibit. If the network administrator created a standard ACL that allows only devices that connect to the R2 G0/0 network access to the devices on the R1 G0/1 interface, how should the ACL be applied?
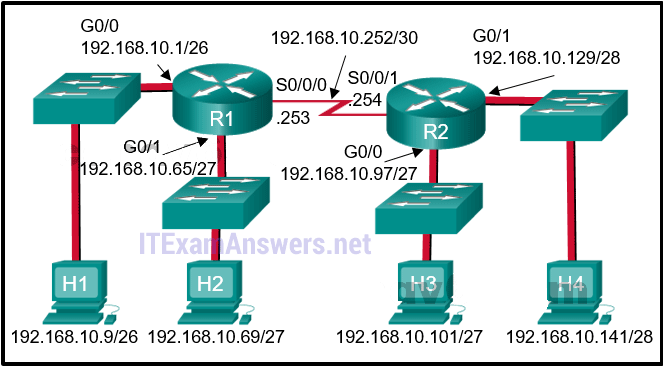
- inbound on the R2 G0/0 interface
- outbound on the R1 G0/1 interface
- inbound on the R1 G0/1 interface
- outbound on the R2 S0/0/1 interface
Explanation: Because standard access lists only filter on the source IP address, they are commonly placed closest to the destination network. In this example, the source packets will be coming from the R2 G0/0 network. The destination is the R1 G0/1 network. The proper ACL placement is outbound on the R1 G0/1 interface.
29. Which is a characteristic of a Type 2 hypervisor?
- does not require management console software
- has direct access to server hardware resources
- best suited for enterprise environments
- installs directly on hardware
30. What are the two types of VPN connections? (Choose two.)
- PPPoE
- Frame Relay
- site-to-site
- remote access
- leased line
Explanation: PPPoE, leased lines, and Frame Relay are types of WAN technology, not types of VPN connections.
31. Refer to the exhibit. What three conclusions can be drawn from the displayed output? (Choose three.)
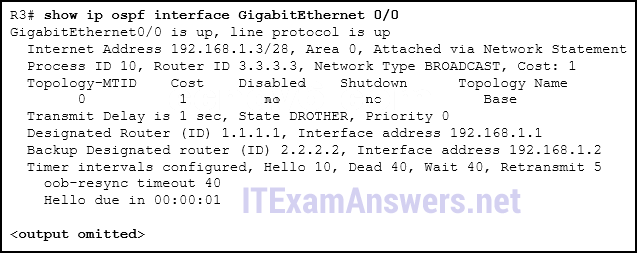
- The DR can be reached through the GigabitEthernet 0/0 interface.
- There have been 9 seconds since the last hello packet sent.
- This interface is using the default priority.
- The router ID values were not the criteria used to select the DR and the BDR.
- The router ID on the DR router is 3.3.3.3
- The BDR has three neighbors.
32. Refer to the exhibit. A network administrator is configuring an ACL to limit the connection to R1 vty lines to only the IT group workstations in the network 192.168.22.0/28. The administrator verifies the successful Telnet connections from a workstation with IP 192.168.22.5 to R1 before the ACL is applied. However, after the ACL is applied to the interface Fa0/0, Telnet connections are denied. What is the cause of the connection failure?
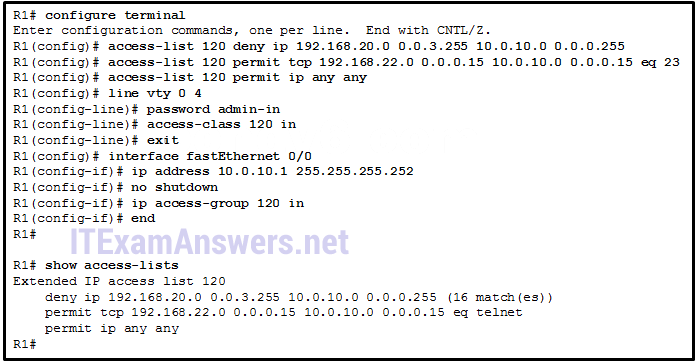
- The enable secret password is not configured on R1.
- The IT group network is included in the deny statement.
- The permit ACE specifies a wrong port number.
- The permit ACE should specify protocol ip instead of tcp.
- The login command has not been entered for vty lines.
Explanation: The source IP range in the deny ACE is 192.168.20.0 0.0.3.255, which covers IP addresses from 192.168.20.0 to 192.168.23.255. The IT group network 192.168.22.0/28 is included in the 192.168.20/22 network. Therefore, the connection is denied. To fix it, the order of the deny and permit ACE should be switched.
33. What functionality does mGRE provide to the DMVPN technology?
- It allows the creation of dynamically allocated tunnels through a permanent tunnel source at the hub and dynamically allocated tunnel destinations at the spokes.
- It provides secure transport of private information over public networks, such as the Internet.
- It is a Cisco software solution for building multiple VPNs in an easy, dynamic, and scalable manner.
- It creates a distributed mapping database of public IP addresses for all VPN tunnel spokes.
Explanation: DMVPN is built on three protocols, NHRP, IPsec, and mGRE. NHRP is the distributed address mapping protocol for VPN tunnels. IPsec encrypts communications on VPN tunnels. The mGRE protocol allows the dynamic creation of multiple spoke tunnels from one permanent VPN hub.
34. What is used to pre-populate the adjacency table on Cisco devices that use CEF to process packets?
- the FIB
- the routing table
- the ARP table
- the DSP
35. What command would be used as part of configuring NAT or PAT to display information about NAT configuration parameters and the number of addresses in the pool?
- show running-config
- show ip nat statistics
- show ip cache
- show version
36. What is a purpose of establishing a network baseline?
- It provides a statistical average for network performance.
- It creates a point of reference for future network evaluations.
- It manages the performance of network devices.
- It checks the security configuration of network devices.
Explanation: A baseline is used to establish normal network or system performance. It can be used to compare with future network or system performances in order to detect abnormal situations.
37. Match the type of WAN device or service to the description. (Not all options are used.)
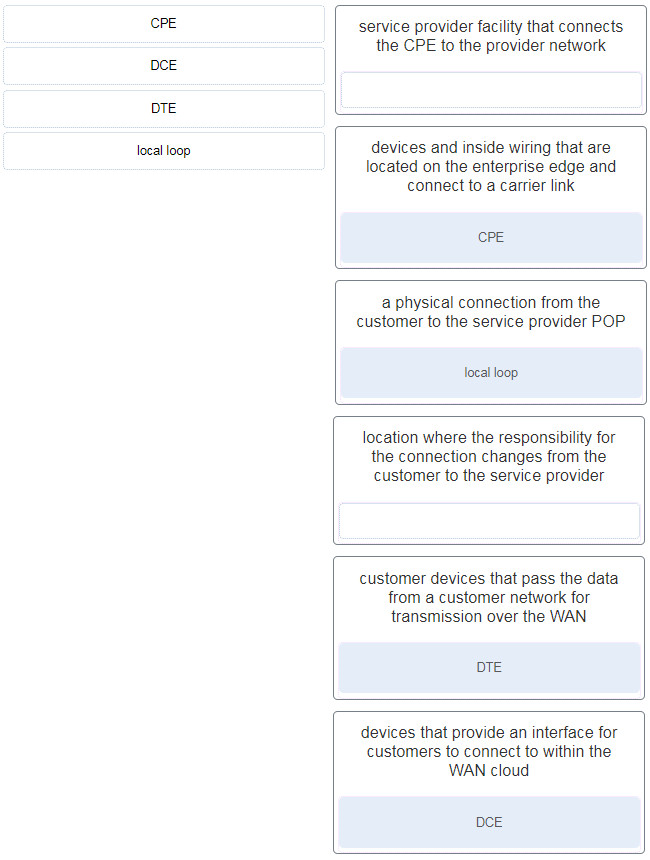
CPE —> devices and inside wiring that are located on the enterprise edge and connect to a carrier link
DCE —> devices that provide an interface for customers to connect to within the WAN cloud
DTE —> customer devices that pass the data from a customer network for transmission over the WAN
local loop —> a physical connection from the customer to the service provider POP
38. Which statement describes a characteristic of standard IPv4 ACLs?
- They filter traffic based on source IP addresses only.
- They can be created with a number but not with a name.
- They are configured in the interface configuration mode.
- They can be configured to filter traffic based on both source IP addresses and source ports.
39. Refer to the exhibit. R1 is configured for NAT as displayed. What is wrong with the configuration?
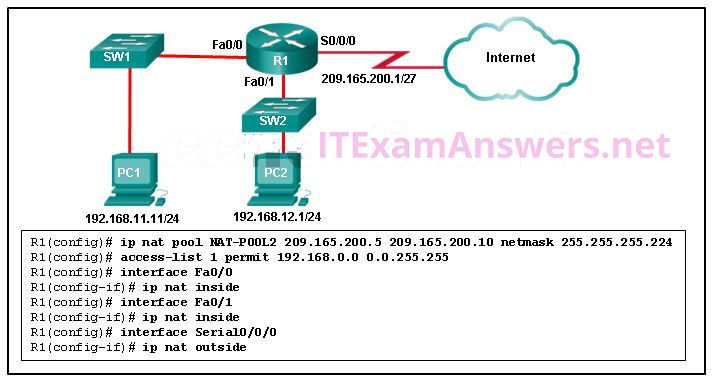
- NAT-POOL2 is not bound to ACL 1.
- Interface Fa0/0 should be identified as an outside NAT interface.
- The NAT pool is incorrect.
- Access-list 1 is misconfigured.
Explanation: R1 has to have NAT-POOL2 bound to ACL 1. This is accomplished with the command R1(config)#ip nat inside source list 1 pool NAT-POOL2. This would enable the router to check for all interesting traffic and if it matches ACL 1 it would be translated by use of the addresses in NAT-POOL2.
40. Refer to the exhibit. What method can be used to enable an OSPF router to advertise a default route to neighboring OSPF routers?
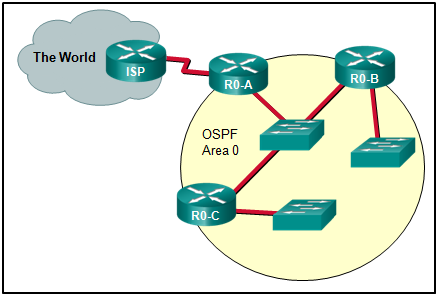
- Use a static route pointing to the ISP and redistribute it.
- Use the redistribute static command on R0-A.
- Use the default-information originate command on ISP.
- Use the default-information originate command on R0-A.
41. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use applications such as John the Ripper,THC Hydra, RainbowCrack, and Medusa?
- to capture and analyze packets within traditional Ethernet LANs or WLANs
- to probe and test the robustness of a firewall by using specially created forged packets
- to make repeated guesses in order to crack a password
42. What are two syntax rules for writing a JSON array? (Choose two.)
- Each value in the array is separated by a comma.
- The array can include only one value type.
- A space must separate each value in the array.
- A semicolon separates the key and list of values.
- Values are enclosed in square brackets.
43. What is a characteristic of a Trojan horse as it relates to network security?
- An electronic dictionary is used to obtain a password to be used to infiltrate a key network device.
- Malware is contained in a seemingly legitimate executable program.
- Extreme quantities of data are sent to a particular network device interface.
- Too much information is destined for a particular memory block, causing additional memory areas to be affecte
Explanation: A Trojan horse carries out malicious operations under the guise of a legitimate program. Denial of service attacks send extreme quantities of data to a particular host or network device interface. Password attacks use electronic dictionaries in an attempt to learn passwords. Buffer overflow attacks exploit memory buffers by sending too much information to a host to render the system inoperable.
44. An attacker is redirecting traffic to a false default gateway in an attempt to intercept the data traffic of a switched network. What type of attack could achieve this?
- TCP SYN flood
- DNS tunneling
- DHCP spoofing
- ARP cache poisoning
Explanation: In DHCP spoofing attacks, an attacker configures a fake DHCP server on the network to issue DHCP addresses to clients with the aim of forcing the clients to use a false default gateway, and other false services. DHCP snooping is a Cisco switch feature that can mitigate DHCP attacks. MAC address starvation and MAC address snooping are not recognized security attacks. MAC address spoofing is a network security threat.
45. A company is developing a security policy for secure communication. In the exchange of critical messages between a headquarters office and a branch office, a hash value should only be recalculated with a predetermined code, thus ensuring the validity of data source. Which aspect of secure communications is addressed?
- data integrity
- non-repudiation
- origin authentication
- data confidentiality
Explanation: Secure communications consists of four elements:
Data confidentiality – guarantees that only authorized users can read the message
Data integrity – guarantees that the message was not altered
Origin authentication – guarantees that the message is not a forgery and does actually come from whom it states
Data nonrepudiation – guarantees that the sender cannot repudiate, or refute, the validity of a message sent
46. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use packet sniffers?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to detect any evidence of a hack or malware in a computer or network
- to probe and test the robustness of a firewall by using specially created forged packets
- to capture and analyze packets within traditional Ethernet LANs or WLANs
47. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 172.20.0.0 255.255.252.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.15.255
- 0.0.3.255
- 0.0.7.255
- 0.0.1.255
48. Match the HTTP method with the RESTful operation.
POST –>> Create
GET –>> Read
PUT/PATCH –>> Update/Replace?Modify
Delete –>> Delete
49. Refer to the exhibit. What is the OSPF cost to reach the West LAN 172.16.2.0/24 from East?
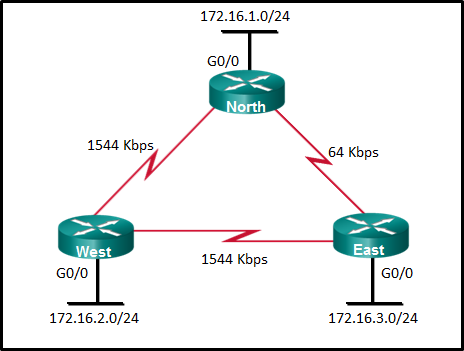
- 782
- 74
- 128
- 65
50. What is one reason to use the ip ospf priority command when the OSPF routing protocol is in use?
- to activate the OSPF neighboring process
- to influence the DR/BDR election process
- to provide a backdoor for connectivity during the convergence process
- to streamline and speed up the convergence process
51. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 210 permit tcp 172.18.20.0 0.0.0.31 172.18.20.32 0.0.0.31 eq ftp .
If a packet with a source address of 172.18.20.14, a destination address of 172.18.20.40, and a protocol of 21 is received on the interface, is the packet permitted or denied?
- permitted
52. What is a characteristic of the two-tier spine-leaf topology of the Cisco ACI fabric architecture?
- The spine and leaf switches are always linked through core switches.
- The spine switches attach to the leaf switches and attach to each other for redundancy.
- The leaf switches always attach to the spines and they are interlinked through a trunk line.
- The leaf switches always attach to the spines, but they never attach to each other.
53. Which two scenarios would result in a duplex mismatch? (Choose two.)
- connecting a device with autonegotiation to another that is manually set to full-duplex
- starting and stopping a router interface during a normal operation
- connecting a device with an interface running at 100 Mbps to another with an interface running at 1000 Mbps
- configuring dynamic routing incorrectly
- manually setting the two connected devices to different duplex modes
54. A network technician is configuring SNMPv3 and has set a security level of auth . What is the effect of this setting?
- authenticates a packet by a string match of the username or community string
- authenticates a packet by using either the HMAC with MD5 method or the SHA method
- authenticates a packet by using either the HMAC MD5 or 3.HMAC SHA algorithms and encrypts the packet with either the DES, 3DES or AES algorithms
- authenticates a packet by using the SHA algorithm only
Explanation: For enabling SNMPv3 one of three security levels can be configured:
1) noAuth
2) auth
3) priv
The security level configured determines which security algorithms are performed on SNMP packets. The auth security level uses either HMAC with MD5 or SHA.
55. What are two types of attacks used on DNS open resolvers? (Choose two.)
- amplification and reflection
- resource utilization
- fast flux
- ARP poisoning
- cushioning
Explanation: Three types of attacks used on DNS open resolvers are as follows:DNS cache poisoning – attacker sends spoofed falsified information to redirect users from legitimate sites to malicious sites
DNS amplification and reflection attacks – attacker sends an increased volume of attacks to mask the true source of the attack
DNS resource utilization attacks – a denial of service (DoS) attack that consumes server resources
56. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit udp 192.168.100.0 0.0.2.255 64.100.40.0 0.0.0.15 eq telnet .
If a packet with a source address of 192.168.101.45, a destination address of 64.100.40.4, and a protocol of 23 is received on the interface, is the packet permitted or denied?
- denied
- permitted
Case 2:
access-list 101 permit udp 192.168.100.0 0.0.2.255 64.100.40.0 0.0.0.0.15 eq telnet .
If a packet with a source address of 192.168.100.219, a destination address of 64.100.40.10, and a protocol of 54 is received on the interface, is the packet permitted or denied?
- denied
- permitted
57. Which type of resources are required for a Type 1 hypervisor?
- a dedicated VLAN
- a management console
- a host operating system
58. In JSON, what is held within square brackets [ ]?
- nested values
- key/value pairs
- an object
- an array
59. What are three components used in the query portion of a typical RESTful API request? (Choose three.)
- resources
- protocol
- API server
- format
- key
- parameters
60. A user reports that when the corporate web page URL is entered on a web browser, an error message indicates that the page cannot be displayed. The help-desk technician asks the user to enter the IP address of the web server to see if the page can be displayed. Which troubleshooting method is being used by the technician?
- top-down
- bottom-up
- divide-and-conquer
- substitution
61. Which protocol provides authentication, integrity, and confidentiality services and is a type of VPN?
- MD5
- AES
- IPsec
- ESP
62. Which statement describes a characteristic of Cisco Catalyst 2960 switches?
- They are best used as distribution layer switches.
- New Cisco Catalyst 2960-C switches support PoE pass-through.
- They are modular switches.
- They do not support an active switched virtual interface (SVI) with IOS versions prior to 15.x.
63. Which component of the ACI architecture translates application policies into network programming?
- the hypervisor
- the Application Policy Infrastructure Controller
- the Nexus 9000 switch
- the Application Network Profile endpoints
64. Which two pieces of information should be included in a logical topology diagram of a network? (Choose two.)
- device type
- cable specification
- interface identifier
- OS/IOS version
- connection type
- cable type and identifier
65. Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem?

- The NAT pool has been exhausted.
- The wrong netmask was used on the NAT pool.
- Access-list 1 has not been configured properly.
- The inside and outside interfaces have been configured backwards.
Explanation: The output of show ip nat statistics shows that there are 2 total addresses and that 2 addresses have been allocated (100%). This indicates that the NAT pool is out of global addresses to give new clients. Based on the show ip nat translations, PCs at 10.1.1.33 and 10.1.1.123 have used the two available addresses to send ICMP messages to a host on the outside network.
66. What are two benefits of using SNMP traps? (Choose two.)
- They eliminate the need for some periodic polling requests.
- They reduce the load on network and agent resources.
- They limit access for management systems only.
- They can provide statistics on TCP/IP packets that flow through Cisco devices.
- They can passively listen for exported NetFlow datagrams.
67. Which statement accurately describes a characteristic of IPsec?
- IPsec works at the application layer and protects all application data.
- IPsec is a framework of standards developed by Cisco that relies on OSI algorithms.
- IPsec is a framework of proprietary standards that depend on Cisco specific algorithms.
- IPsec works at the transport layer and protects data at the network layer.
- IPsec is a framework of open standards that relies on existing algorithms.
Explanation: IPsec can secure a path between two network devices. IPsec can provide the following security functions:
Confidentiality – IPsec ensures confidentiality by using encryption.
Integrity – IPsec ensures that data arrives unchanged at the destination using a hash algorithm, such as MD5 or SHA.
Authentication – IPsec uses Internet Key Exchange (IKE) to authenticate users and devices that can carry out communication independently. IKE uses several types of authentication, including username and password, one-time password, biometrics, pre-shared keys (PSKs), and digital certificates.
Secure key exchange- IPsec uses the Diffie-Hellman (DH) algorithm to provide a public key exchange method for two peers to establish a shared secret key.
68. In a large enterprise network, which two functions are performed by routers at the distribution layer? (Choose two.)
- connect users to the network
- provide a high-speed network backbone
- connect remote networks
- provide Power over Ethernet to devices
- provide data traffic security
69. Which two statements describe the use of asymmetric algorithms? (Choose two.)
- Public and private keys may be used interchangeably.
- If a public key is used to encrypt the data, a public key must be used to decrypt the data.
- If a private key is used to encrypt the data, a public key must be used to decrypt the data.
- If a public key is used to encrypt the data, a private key must be used to decrypt the data.
- If a private key is used to encrypt the data, a private key must be used to decrypt the data.
Explanation: Asymmetric algorithms use two keys: a public key and a private key. Both keys are capable of the encryption process, but the complementary matched key is required for decryption. If a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
70. Refer to the exhibit. A network administrator has deployed QoS and has configured the network to mark traffic on the VoIP phones as well as the Layer 2 and Layer 3 switches. Where should initial marking occur to establish the trust boundary?
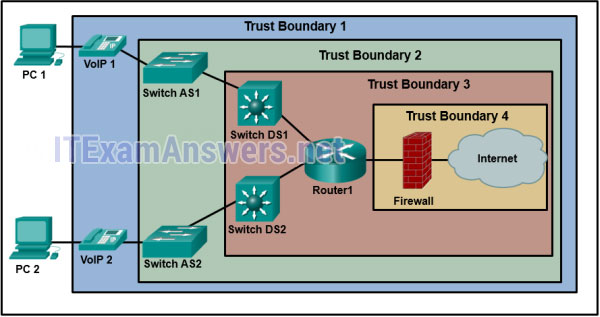
- Trust Boundary 4
- Trust Boundary 3
- Trust Boundary 1
- Trust Boundary 2
Explanation: Traffic should be classified and marked as close to its source as possible. The trust boundary identifies at which device marked traffic should be trusted. Traffic marked on VoIP phones would be considered trusted as it moves into the enterprise network.
71. What are two benefits of extending access layer connectivity to users through a wireless medium? (Choose two.)
- reduced costs
- decreased number of critical points of failure
- increased flexibility
- increased bandwidth availability
- increased network management options
72. What are two purposes of launching a reconnaissance attack on a network? (Choose two.)
- to scan for accessibility
- to retrieve and modify data
- to gather information about the network and devices
- to prevent other users from accessing the system
- to escalate access privileges
73. A group of users on the same network are all complaining about their computers running slowly. After investigating, the technician determines that these computers are part of a zombie network. Which type of malware is used to control these computers?
- botnet
- spyware
- virus
- rootkit
74. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit tcp 10.1.1.0 0.0.0.255 host 192.31.7.45 eq dns .
If a packet with a source address of 10.1.1.201, a destination address of 192.31.7.45, and a protocol of 23 is received on the interface, is the packet permitted or denied?
- permitted
- denied
75. Refer to the exhibit. From which location did this router load the IOS?
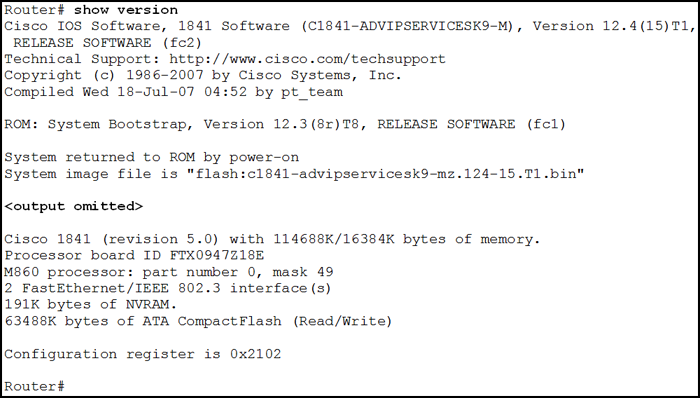
- flash memory
- NVRAM?
- RAM
- ROM
- a TFTP server?
76. Refer to the exhibit. Which data format is used to represent the data for network automation applications?
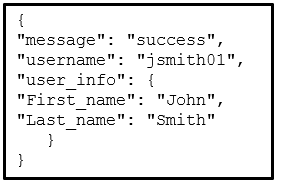
- XML
- YAML
- HTML
- JSON
Explanation: The common data formats that are used in many applications including network automation and programmability are as follows:
- JavaScript Object Notation (JSON) – In JSON, the data known as an object is one or more key/value pairs enclosed in braces { }. Keys must be strings within double quotation marks ” “. Keys and values are separated by a colon.
- eXtensible Markup Language (XML) – In XML, the data is enclosed within a related set of tags data.
- YAML Ain’t Markup Language (YAML) – In YAML, the data known as an object is one or more key value pairs. Key value pairs are separated by a colon without the use of quotation marks. YAML uses indentation to define its structure, without the use of brackets or commas.
77. What QoS step must occur before packets can be marked?
- classifying
- shaping
- queuing
- policing
78. What is the main function of a hypervisor?
- It is used to create and manage multiple VM instances on a host machine.
- It is a device that filters and checks security credentials.
- It is a device that synchronizes a group of sensors.
- It is software used to coordinate and prepare data for analysis.
- It is used by ISPs to monitor cloud computing resources.
79. A company needs to interconnect several branch offices across a metropolitan area. The network engineer is seeking a solution that provides high-speed converged traffic, including voice, video, and data on the same network infrastructure. The company also wants easy integration to their existing LAN infrastructure in their office locations. Which technology should be recommended?
- Frame Relay
- Ethernet WAN
- VSAT
- ISDN
80. Refer to the exhibit. As traffic is forwarded out an egress interface with QoS treatment, which congestion avoidance technique is used?
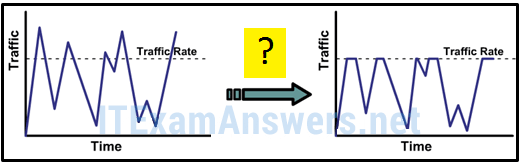
- traffic shaping
- weighted random early detection
- classification and marking
- traffic policing
Explanation: Traffic shaping buffers excess packets in a queue and then forwards the traffic over increments of time, which creates a smoothed packet output rate. Traffic policing drops traffic when the amount of traffic reaches a configured maximum rate, which creates an output rate that appears as a saw-tooth with crests and troughs.
81. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit tcp 10.1.1.0 0.0.0.255 host 10.1.3.8 eq dns .
If a packet with a source address of 10.1.3.8, a destination address of 10.10.3.8, and a protocol of 53 is received on the interface, is the packet permitted or denied?
- denied
- permitted
82. Refer to the exhibit. What is the purpose of the command marked with an arrow shown in the partial configuration output of a Cisco broadband router?
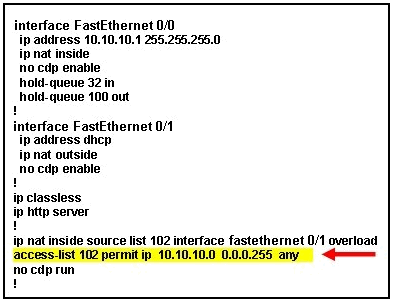
- defines which addresses are allowed into the router
- defines which addresses can be translated
- defines which addresses are assigned to a NAT pool
- defines which addresses are allowed out of the router
83. If a router has two interfaces and is routing both IPv4 and IPv6 traffic, how many ACLs could be created and applied to it?
- 12
- 4
- 8
- 16
- 6
84. Refer to the exhibit. An administrator first configured an extended ACL as shown by the output of the show access-lists command. The administrator then edited this access-list by issuing the commands below.
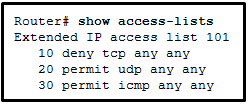
Router(config)# ip access-list extended 101 Router(config-ext-nacl)# no 20 Router(config-ext-nacl)# 5 permit tcp any any eq 22 Router(config-ext-nacl)# 20 deny udp any any
Which two conclusions can be drawn from this new configuration? (Choose two.)
- TFTP packets will be permitted.
- Ping packets will be permitted.
- Telnet packets will be permitted.
- SSH packets will be permitted.
- All TCP and UDP packets will be denied.
Explanation: After the editing, the final configuration is as follows:
Router# show access-lists
Extended IP access list 101
5 permit tcp any any eq ssh
10 deny tcp any any
20 deny udp any any
30 permit icmp any any
So, only SSH packets and ICMP packets will be permitted.
85. Which troubleshooting approach is more appropriate for a seasoned network administrator rather than a less-experienced network administrator?
- a less-structured approach based on an educated guess
- an approach comparing working and nonworking components to spot significant differences
- a structured approach starting with the physical layer and moving up through the layers of the OSI model until the cause of the problem is identified
- an approach that starts with the end-user applications and moves down through the layers of the OSI model until the cause of the problem has been identified
86. Refer to the exhibit. Many employees are wasting company time accessing social media on their work computers. The company wants to stop this access. What is the best ACL type and placement to use in this situation?

- extended ACL outbound on R2 WAN interface towards the internet
- standard ACL outbound on R2 WAN interface towards the internet
- standard ACL outbound on R2 S0/0/0
- extended ACLs inbound on R1 G0/0 and G0/1
87. Refer to the exhibit. An administrator is trying to configure PAT on R1, but PC-A is unable to access the Internet. The administrator tries to ping a server on the Internet from PC-A and collects the debugs that are shown in the exhibit. Based on this output, what is most likely the cause of the problem?
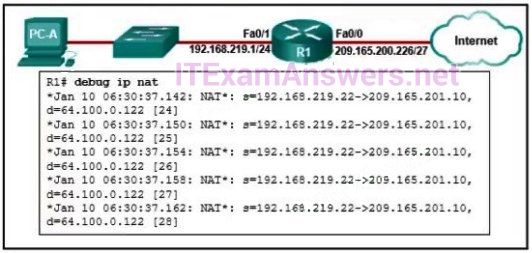
- The inside and outside NAT interlaces have been configured backwards
- The inside global address is not on the same subnet as the ISP
- The address on Fa0/0 should be 64.100.0.1.
- The NAT source access list matches the wrong address range.
Explanation: The output of debug ip nat shows each packet that is translated by the router. The “s” is the source IP address of the packet and the “d” is the destination. The address after the arrow (“->”) shows the translated address. In this case, the translated address is on the 209.165.201.0 subnet but the ISP facing interface is in the 209.165.200.224/27 subnet. The ISP may drop the incoming packets, or might be unable to route the return packets back to the host because the address is in an unknown subnet.
88. Why is QoS an important issue in a converged network that combines voice, video, and data communications?
- Data communications must be given the first priority.
- Voice and video communications are more sensitive to latency.
- Legacy equipment is unable to transmit voice and video without QoS.
- Data communications are sensitive to jitter.
89. Which statement describes a VPN?
- VPNs use logical connections to create public networks through the Internet.
- VPNs use open source virtualization software to create the tunnel through the Internet.
- VPNs use dedicated physical connections to transfer data between remote users.
- VPNs use virtual connections to create a private network through a public network.
90. In which OSPF state is the DR/BDR election conducted?
- ExStart
- Init
- Two-Way
- Exchange
91. Two corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks?
- Cisco Secure Mobility Clientless SSL VPN
- Frame Relay
- remote access VPN using IPsec
- Cisco AnyConnect Secure Mobility Client with SSL
- site-to-site VPN
Explanation: The site-to-site VPN is an extension of a classic WAN network that provides a static interconnection of entire networks. Frame Relay would be a better choice than leased lines, but would be more expensive than implementing site-to-site VPNs. The other options refer to remote access VPNs which are better suited for connecting users to the corporate network versus interconnecting two or more networks.
92. What is the final operational state that will form between an OSPF DR and a DROTHER once the routers reach convergence?
- loading
- established
- full
- two-way
93. Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
- Router R3 will become the DR and router R1 will become the BDR.
- Router R4 will become the DR and router R3 will become the BDR.
- Router R1 will become the DR and router R2 will become the BDR.
- Router R3 will become the DR and router R2 will become the BDR.
Explanation: OSPF elections of a DR are based on the following in order of precedence:
- highest pritority from 1 -255 (0 = never a DR)
- highest router ID
- highest IP address of a loopback or active interface in the absence of a manually configured router ID. Loopback IP addresses take higher precedence than other interfaces.
In this case routers R3 and R1 have the highest router priority. Between the two, R3 has the higher router ID. Therefore, R3 will become the DR and R1 will become the BDR.
94. Which type of server would be used to keep a historical record of messages from monitored network devices?
- DNS
- DHCP
- syslog
- authentication
95. When QoS is implemented in a converged network, which two factors can be controlled to improve network performance for real-time traffic? (Choose two.)
- packet addressing
- delay
- jitter
- packet routing
- link speed
Explanation: Delay is the latency between a sending and receiving device. Jitter is the variation in the delay of the received packets. Both delay and jitter need to be controlled in order to support real-time voice and video traffic.
96. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layer of the network?
- Determine ownership.
- Determine the symptoms.
- Narrow the scope.
- Document the symptoms.
- Gather information.
97. What protocol sends periodic advertisements between connected Cisco devices in order to learn device name, IOS version, and the number and type of interfaces?
- CDP
- SNMP
- NTP
- LLDP
98. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 192.168.0.0 255.255.252.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.0.127
- 0.0.0.31
- 0.0.3.255
- 0.0.0.63
99. Refer to the exhibit. An administrator configures the following ACL in order to prevent devices on the 192.168.1.0 subnet from accessing the server at 10.1.1.5:
access-list 100 deny ip 192.168.1.0 0.0.0.255 host 10.1.1.5 access-list 100 permit ip any any

Where should the administrator place this ACL for the most efficient use of network resources?
- inbound on router A Fa0/0
- outbound on router B Fa0/0
- outbound on router A Fa0/1
- inbound on router B Fa0/1
100. Which type of OSPFv2 packet is used to forward OSPF link change information?
- link-state acknowledgment
- link-state update
- hello
- database description
101. What protocol synchronizes with a private master clock or with a publicly available server on the internet?
- MPLS
- CBWFQ
- TFTP
- NTP
102. Which type of VPN allows multicast and broadcast traffic over a secure site-to-site VPN?
- dynamic multipoint VPN
- SSL VPN
- IPsec virtual tunnel interface
- GRE over IPsec
103. An OSPF router has three directly connected networks; 10.0.0.0/16, 10.1.0.0/16, and 10.2.0.0/16. Which OSPF network command would advertise only the 10.1.0.0 network to neighbors?
- router(config-router)# network 10.1.0.0 0.0.255.255 area 0
- router(config-router)# network 10.1.0.0 0.0.15.255 area 0
- router(config-router)# network 10.1.0.0 255.255.255.0 area 0
- router(config-router)# network 10.1.0.0 0.0.0.0 area 0
104. Refer to the exhibit. Which sequence of commands should be used to configure router A for OSPF?
router ospf 1
network 192.168.10.0 area 0
router ospf 1
network 192.168.10.0
router ospf 1
network 192.168.10.64 255.255.255.192
network 192.168.10.192 255.255.255.252
router ospf 1
network 192.168.10.64 0.0.0.63 area 0
network 192.168.10.192 0.0.0.3 area 0
105. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 192.168.0.0 255.255.254.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.7.255
- 0.0.1.255
- 0.0.3.255
- 0.0.15.255
106. How does virtualization help with disaster recovery within a data center?
- improvement of business practices
- supply of consistent air flow
- support of live migration
- guarantee of power
Explanation: Live migration allows moving of one virtual server to another virtual server that could be in a different location that is some distance from the original data center.
Case 2:
- Less energy is consumed.
- Server provisioning is faster.
- Hardware at the recovery site does not have to be identical to production equipment.
- Power is always provided.
Explanation:&n