Top Hacking and Security Tools
What Is a “Hacker”?
Originally, a hacker was a skilled computer expert who devised clever solutions (“hacks”). Over time, the term evolved to commonly mean a threat actor. Today we distinguish between:
White Hat Hackers (Ethical)
- Use skills legally and ethically (e.g., penetration testing).
- Report vulnerabilities to developers so they can be fixed.
Gray Hat Hackers
- May commit questionable or minor illegal acts without intent for personal gain or damage.
- Might disclose a vulnerability after compromising a system.
Black Hat Hackers (Criminal)
- Compromise security for personal gain or malicious purposes (e.g., data theft, sabotage).
Evolution of Hackers
- 1960s — Phone Phreaking: Exploiting telephone switches using audio tones (e.g., whistles) to place free long-distance calls.
- Mid-1980s — Modems & War Dialing: Automated dialing to find computers, followed by password-cracking to gain access.
Common Threat Actor Types & Terms
- Script Kiddies: Inexperienced users running existing scripts/exploits, usually not for profit.
- Vulnerability Brokers: Often gray hats who discover exploits and report them to vendors for rewards.
- Hacktivists: Gray hats protesting organizations/governments via leaks, posts, or attacks.
- Cybercriminals: Black hats acting solo or within organized cybercrime groups.
- State-Sponsored Hackers: Operate for nation-state interests (can be white or black hats). Targets include foreign governments, terrorist groups, and corporations.
Attack Tools: A Quick Introduction
To exploit a vulnerability, a threat actor needs a technique or tool. Over the years, tools have become more automated and easier to use—which helps defenders test, but also enables attackers.
Evolution of Security Tools
Ethical hacking relies on many tools to validate security. Unfortunately, tools used by defenders can be misused by attackers. Ethical professionals must understand both.
Common Penetration-Testing Tool Categories
Note: This list is not exhaustive; tools evolve constantly.
Password Crackers
Used to recover/crack passwords (by guessing, bypassing encryption, or discovery).
Examples: John the Ripper, Ophcrack, L0phtCrack, THC Hydra, RainbowCrack, Medusa.
Wireless Hacking Tools
Assess wireless networks for security weaknesses.
Examples: Aircrack-ng, Kismet, InSSIDer, KisMAC, Firesheep, NetStumbler.
Network Scanning & Hacking Tools
Probe devices/hosts for open TCP/UDP ports.
Examples: Nmap, SuperScan, Angry IP Scanner, NetScanTools.
Packet Crafting Tools
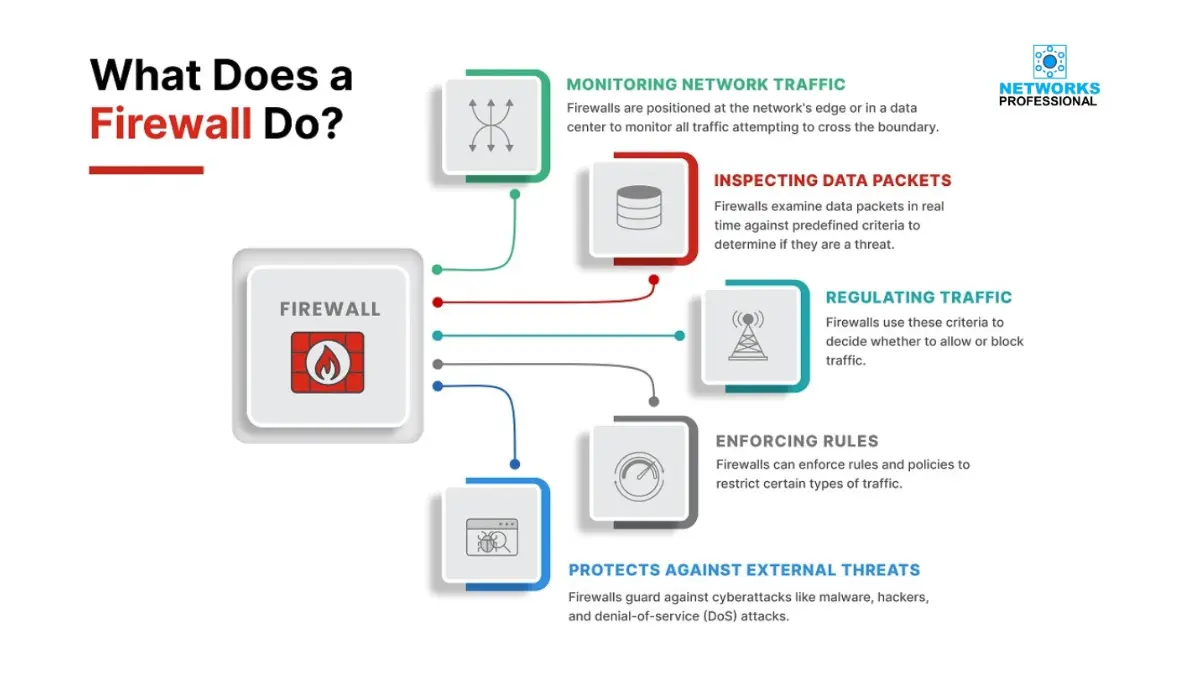
Send specially forged packets to test firewall robustness.
Examples: Hping, Scapy, Socat, Yersinia, Netcat, Nping, Nemesis.
Packet Sniffers
Capture/analyze traffic on LANs/WLANs.
Examples: Wireshark, Tcpdump, Ettercap, Dsniff, EtherApe, Paros, Fiddler, Ratproxy, SSLstrip.
Rootkit Detectors
Check file/directory integrity to detect rootkits.
Examples: AIDE, Netfilter, PF (OpenBSD Packet Filter).
Fuzzers (Vulnerability Discovery)
Automate malformed inputs to find flaws.
Examples: Skipfish, Wapiti, W3af.
Forensic Tools
Find and analyze evidence on systems.
Examples: Sleuth Kit, Helix, Maltego, EnCase.
Debuggers
Reverse-engineering binaries (exploit writing or malware analysis).
Examples: GDB, WinDbg, IDA Pro, Immunity Debugger.
Hacking Operating Systems
Distros preloaded with assessment tools.
Examples: Kali Linux, Knoppix, BackBox Linux.
Encryption Tools
Protect data at rest/in transit via cryptography.
Examples: VeraCrypt, CipherShed, OpenSSH, OpenSSL, Tor, OpenVPN, Stunnel.
Vulnerability Exploitation Frameworks
Identify and exploit known weaknesses.
Examples: Metasploit, Core Impact, sqlmap, Social-Engineer Toolkit (SET), Netsparker.
Vulnerability Scanners
Scan networks/systems for open ports and known CVEs; cover VMs, BYOD, client DBs.
Examples: Nipper, Secunia PSI, Core Impact, Nessus v6, SAINT, OpenVAS.
Platform Note
Many tools are UNIX/Linux-based. Security professionals should maintain a strong UNIX/Linux background.
Ethical Use & Compliance
This outline is for defensive security and awareness. Use tools only with authorization, follow laws and policies, and adhere to responsible disclosure practices.
You can also read :Common Network Attacks